Konzepterstellung
Abstecken des Project Scope und evaluieren des Status quo, bestehender Hard- und Software durch unsere Projektmanager
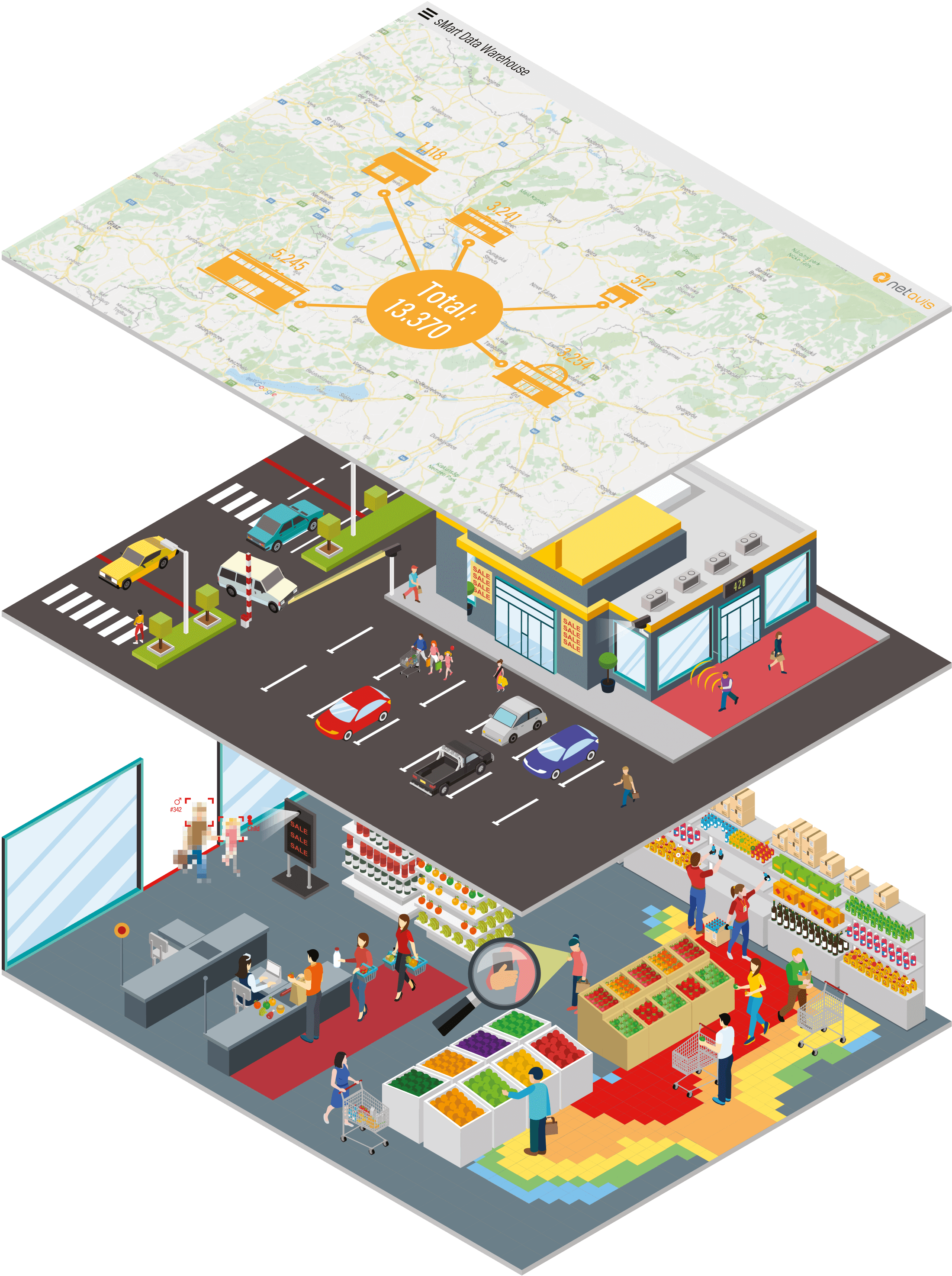
Sie können in der Kartenansicht leicht zwischen den Standorten navigieren und Daten in der Gesamtheit oder standortspezifisch darstellen.
In Kombination mit der Frequenz einfahrender Fahrzeuge können Sie Ihre Turn-In Rate berechnen und Marketingaktionen im Außenbereich optimieren.
Die Informationen sind für eine zielgruppengesteuerte Ansprache der Kunden im Store oder als Statistik verfügbar.
Der Re-Use Ihrer bereits bestehenden CCTV-Hardware für Geschäftsanwendungen bietet der Anlage weiteres Potential.
Mit den Zählstatistiken können Sie Turn-In Rates für Ein- und Ausgänge berechnen.
Kunden mittels Gesichtsdetektion nach Alter und Geschlecht segmentieren oder Kinder und Erwachsene anhand ihrer Körpergrößen unterscheiden
Werbung dynamisch auf Verweildauer, Kundenanzahl und demographische Segmentierungsdaten anpassen.
Sie können anhand der Attention Time auch die Attraktivität des Contents messen.
Mit den Zählstatistiken können Sie Turn-In Rates für Ein- und Ausgänge berechnen.
Sie können im sMart Ihre Geschäftsdaten miteinander kombinieren, um eine detaillierte Analyse durchzuführen.
Werden bestimmte Warteschlangenlängen überschritten, kann sich automatisch eine zusätzliche Kasse öffnen. Zu Zonen, wo sich Kunden besonders lange aufhalten, kann automatisch ein Mitarbeiter geschickt werden.
Entdecken Sie bevorzugte/vernachlässigte Bereiche, Trends und typische Verhaltensmuster.
Daten von Mobilfunkanbietern enthalten Informationen über Geographische Daten, Alter und Geschlecht.
Die Detektion von Mitarbeiten erfolgt nicht personalisiert.
sMart sammelt Daten aus unterschiedlichen Sensoren und Systemen für unterschiedliche Anwendungen.
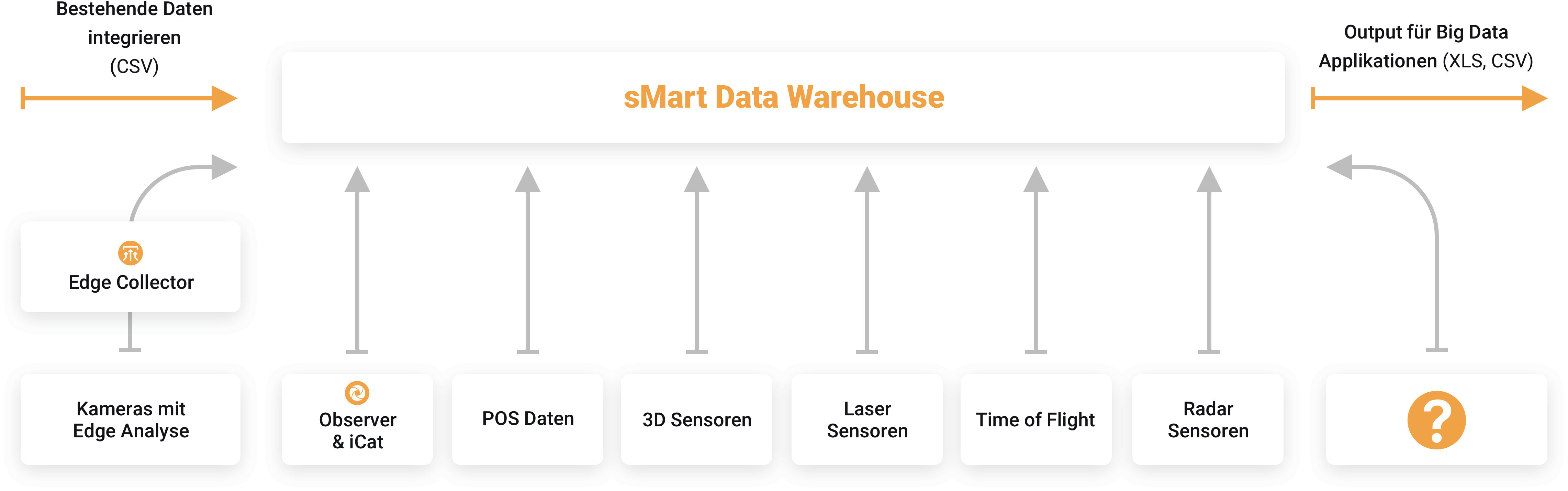
z.B. Zähldaten aus bestehenden Sensoren
Sammelt Daten und stellt diese in der Cloud zur Verfügung
Videoanalyse direkt auf der Kamera
Daten aus Serverbasierter Videoanalyse
Geschäfsdaten aus POS-Systemen
Hochgenaue Zähldaten
Zuverlässige Detektion von Objekten ohne datenschutzrelevante Einschränkungen
Zuverlässige Detektion von Objekten ohne datenschutzrelevante Einschränkungen und die Möglichkeit Verkaufspersonal zu exkludieren
Zuverlässige Detektion von Objekten ohne datenschutzrelevante Einschränkungen
Zukünftige Technologien
Gesammelte Daten für Big Data Applikationen aufbereiten und exportieren
Für die zentralisierte
Koordination von Filialen
Für simultane Kontrolle und
separaten Zugriff auf Daten
Für kleine Systeme mit
vollständiger Funktionalität
Abstecken des Project Scope und evaluieren des Status quo, bestehender Hard- und Software durch unsere Projektmanager
Falls nötig auch die Beschaffung zusätzlicher Hardware durch Netavis Partner
Inklusive Einführung und Inbetriebnahme der Infrastruktur
After Sales Service Agreements und Lizenzen für Software Updates
Klicken Sie sich durch und sehen Sie, welche Daten Ihnen ohne
unsere Systeme entgehen
„Demo starten“ klicken
Username und Passwort eingeben